Table of Contents
Feature of Ethernet network encryption dog for IP cameras
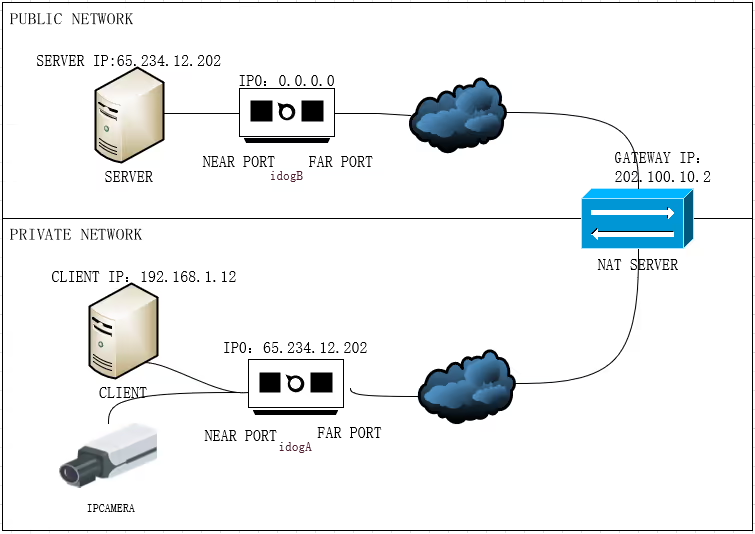
- Network encryption idog,
- support public network to public network, public network to private network,
- private network to private network encryption communication AES encryption,
- key length 128 bits, 192 bits, 256 bits small, safe and reliable
- Internet data encryption, internet encryption dog.
Ethernet Encryption refers to the methods used to secure data transmitted over an Ethernet network. Ethernet, as a wired communication standard, provides high-speed data transfer but is not inherently encrypted. To secure Ethernet traffic, various encryption techniques and protocols are implemented.
Common Encryption Techniques for Ethernet
- MACsec (Media Access Control Security):
- A Layer 2 security protocol that provides point-to-point encryption for Ethernet links.
- Ensures confidentiality, integrity, and authenticity of data between devices on the same LAN.
- Widely supported in enterprise networking equipment.
- IPsec (Internet Protocol Security):
- Operates at Layer 3, typically used for securing data over routed networks.
- Can encrypt Ethernet traffic when combined with tunneling protocols like GRE (Generic Routing Encapsulation).
- TLS/SSL (Transport Layer Security / Secure Sockets Layer):
- Often used at higher layers for specific applications but can secure Ethernet traffic indirectly when data is encapsulated within application protocols like HTTPS.
- VPNs (Virtual Private Networks):
- Encrypt Ethernet traffic across insecure or public networks.
- Common protocols include OpenVPN, WireGuard, and L2TP/IPsec.
- Encryption in Ethernet-over-Fiber Networks:
- Encryption mechanisms tailored to high-speed fiber-optic Ethernet links, often integrated with hardware.
Description Box Example
If you’re creating a description box for Ethernet encryption, here’s a template you might use:
Ethernet Encryption Overview
Ethernet encryption secures data transmitted over wired Ethernet networks to protect it from interception or tampering. Common methods include MACsec for link-layer security, IPsec for encrypted routing, and VPNs for encrypted tunneling across public or private networks. These technologies ensure data confidentiality, integrity, and authenticity in various network environments.
Applications:
- Enterprise LAN security
- Secure data centers and cloud connections
- Industrial control systems
- Government and military communications
Benefits:
- Prevents unauthorized access to sensitive data
- Protects against man-in-the-middle (MITM) attacks
Perhaps you’re also interested in the CVBS camera’s encryption and description module? I would appreciate it if you could check Vcan2028.





Ask A Question
Thank you for your response. ✨