Advanced Encryption Standard (Advanced Encryption Standard, abbreviation: AES), this standard is used to replace the original DES and is widely used all over the world.
AES can encrypt and decrypt quickly in software and hardware, is relatively easy to implement, and requires only a small amount of memory. It is currently being deployed to a wider range.
- What are the main difference and security levels between AES128 and AES256?
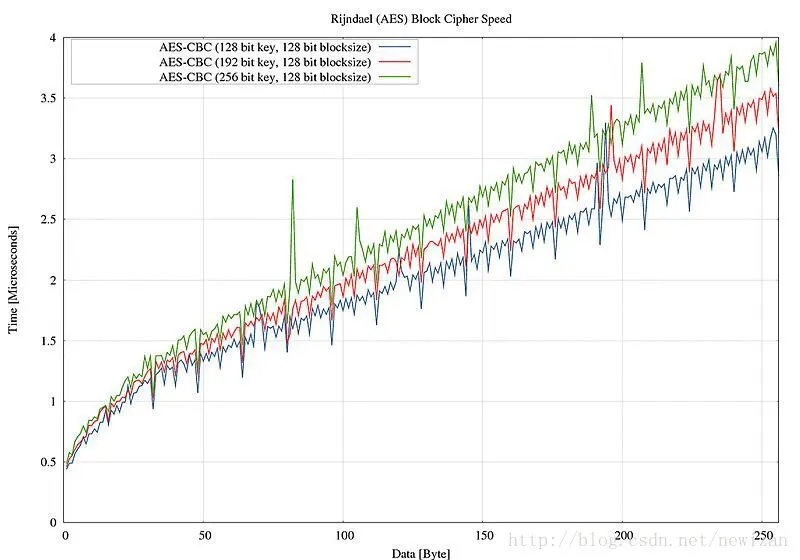
- What is their consumption on the machine?
- What is the performance of the two?
- How to choose for actual development?
AES is very fast compared to similar symmetric encryption algorithms. For example, an x86 server with AES-NI can at least reach a speed of several hundred M/s. Security is basically equivalent for the foreseeable future, as even 128-bit is complex enough not to be brute-forced. At present, 112-bit passwords are still in commercial use, and 128-bit is tens of thousands of times that of 112-bit, so it is more cost-effective to use 128-bit in practice (slightly saves resources).
AES256 takes about 40% more time than AES128, for the extra 4 rounds of round key generation and the corresponding SPN operation. In addition, generating 256-bit keys may also require more overhead than 128-bit keys, but this part of the overhead should be negligible.
The degree of security is naturally AES256 safer than AES128 because currently there is no very effective algebraic attack method except for brute force cracking.
There are specific attack methods for specific software/hardware implementations of AES-256 or AES-128, so it is not easy to generalize.
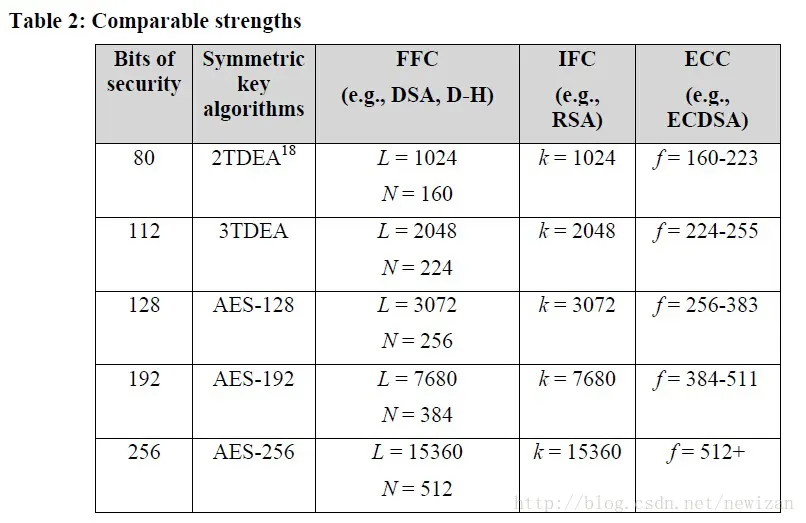
Modern cryptography is divided into symmetric encryption and asymmetric encryption (public key encryption), and the representative algorithms are DES (now developed into 3DES), AES, and RSA. The resource consumption of asymmetric encryption algorithms is greater than that of symmetric encryption. Generally, hybrid encryption processing is performed, for example, RSA is used for key distribution and negotiation, and AES is used for encryption and decryption of business data.
Some pictures related to some encryption and decryption symmetric and asymmetric algorithms:
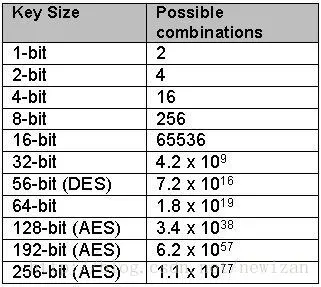
Regarding whether to use the AES128 or AES256 algorithm, I personally think that AES128 is enough, of course, AES256 can be used as a marketing tool.





Ask A Question
Thank you for your response. ✨