數據完整性, 重放攻擊防護, 和無人機無線視訊數據鏈路中的協議詳細信息
目錄
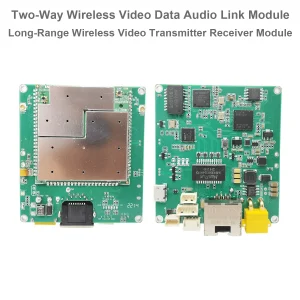
概觀
將無線視訊資料鏈路整合到專業系統(例如無人機)時, 機器人技術, 或遠端視訊傳輸平台—工程師經常提出以下問題 資料完整性, 重播攻擊保護, 和 乙太網路通訊協定的安全性.
本文為客戶的常見問題提供了明確的答案, 基於我們工程團隊的詳細技術解釋.
1. 您的無線視訊資料連結如何確保傳輸訊息的完整性?
我們的無人機基於 OFDM 的無線視訊資料鏈路採用 透明傳輸架構. 串口和網口皆作為 透明頻道, 意義:
- 無論空中側發射器輸入什麼數據,都會將其原封不動地傳送到地面側接收器.
- 系統不修改, 壓縮, 或以任何方式解釋數據.
- 它不會插入額外的元數據,例如時間戳, 序號, 或加密訊息.
這種方法背後的設計理念是實現 超低延遲 和 最大相容性. 透過消除不必要的處理層, 系統可以將延遲維持在低至 30 毫秒, 使其成為即時視訊的理想選擇, 控制, 和遙測應用.
然而, 這也意味著 訊息完整性驗證 不由資料鏈路本身處理. 任何檢測或防止資料篡改的機制都應在使用者自己的應用程式層中實現.
2. 您的系統能否抵禦重播攻擊?
當惡意行為者捕獲有效的資料傳輸並隨後重播它以欺騙接收系統時,就會發生重播攻擊.
我們的無線視訊數據鏈路, 成為一座透明的橋樑, 做 不包括針對重播攻擊的內建保護. 它在收到數據時轉發所有數據, 沒有時間戳驗證或身份驗證檢查.
如果需要防止重播攻擊, 我們建議實施以下解決方案之一 應用層或網路層:
- 新增時間戳或序號 在每個資料幀內,允許接收器檢測重複或延遲的資料包.
- 使用加密和身份驗證機制 例如 TLS (傳輸層安全) 或DTLS (資料封包傳輸層安全協定).
- 採用挑戰-回應協議 發送器和接收器之間確認訊息的新鮮度.
這種方法允許開發人員根據自己的操作要求自訂安全功能,而不會影響無線鏈路的核心傳輸性能.
3. 您的系統在資料中是否包含任何時間戳信息?
沒有. 資料鏈路在傳輸的資料流中不嵌入任何時間戳記或時間相關訊息.
如果您的應用程式需要同步或事件追蹤, 你可以 新增時間戳標頭 到你自己的資料包. 例如, 您可以在每個串列資料幀前面新增一個包含時間戳記或序列計數器的小標頭.
此方法允許接收系統驗證訊息順序, 計算延遲, 並檢測潛在的重播嘗試.
4. 乙太網路通訊中是否使用 TLS 或任何其他加密協議?
預設情況下, 我們的乙太網路介面使用 標準透明IP傳輸-那是, 原始資料包在沒有封裝或加密的情況下傳輸.
有 無 TLS 或 DTLS 層 內建於無線鏈路模組本身. 這種設計確保了與各種資料類型的兼容性 (視頻流, 遙測, 命令包, 等等) 並允許使用者自由定義自己喜歡的通訊協議.
如果需要加密或訊息認證, 使用者可以在自己的軟體中輕鬆實現這些安全層. 例如:
- 使用 帶有 TLS 的 TCP 確保可靠性和保密性.
- 使用 具有應用程式層級完整性檢查的 UDP (CRC, 哈馬卡, 等等) 在保持部分保護的同時降低延遲.
5. 如果無線訊號變弱或斷開會發生什麼情況?
如果無線鏈路訊號品質下降或暫時斷開, 任何無法傳輸的資料都將被簡單地 丟棄的.
系統確實 不緩衝或重傳 未發送的數據. 這確保了資料流保持即時並且沒有延遲累積, 這對於 無人機飛行控制, 實時視頻傳輸, 和即時遙測.
如果您的應用程式需要保證交付或緩衝, 你可以切換到 基於TCP的通信, 因為 TCP/IP 提供內建的重傳和流量控制機制.
6. 您能否提供系統檢測到資料竄改的證據?
由於連結執行 原始透明轉發, 它本身不會檢測或記錄資料篡改.
如果您想驗證訊息完整性, 您應該添加自己的應用程式級別檢查, 如:
- CRC (循環冗餘檢查) 用於基本資料完整性驗證;
- 哈馬卡 (基於哈希的消息驗證碼) 用於更強的身份驗證和篡改檢測;
- 數位簽名 是否必須以加密方式保證資料真實性.
這些措施允許接收者檢測傳輸過程中可能發生的任何未經授權的修改.
7. 乙太網路通訊採用什麼協議?
乙太網路通訊基於 標準IP網路協定. 系統不會將資料封裝成任何特定的進階格式,例如 TLS, 資料傳輸層安全, 或專有加密.
簡單來說, 該設備充當串行或基於 IP 的介面之間的透明橋樑. 您可以傳輸視訊串流 (例如, 即時傳輸/即時傳輸協議), 遙測數據, 或直接透過它自訂 TCP/UDP 封包.
這種靈活性使開發人員能夠將無線鏈路整合到各種系統中,從無人機有效載荷和萬向節到監控和工業控制應用.
8. 概括
我們的無人機無線視訊數據鏈路設計為 高穩定性, 超低延遲, 以及透明的數據傳輸 考慮到.
總結一下:
| 特徵 | 內建 | 使用者可實施 |
|---|---|---|
| 時間戳 / 重播保護 | ❌ 不包括在內 | ✅ 透過應用層添加 |
| 資料加密 (傳輸層安全/資料傳輸層) | ❌ 不包括在內 | ✅ 透過用戶軟體支持 |
| 訊息完整性檢查 | ❌ 不包括在內 | ✅ 透過 CRC 實現 / 哈馬卡 |
| 緩衝 / 重傳 | ❌ 不包括在內 | ✅ 使用 TCP 進行緩衝 |
| 潛伏 | ✅ 超低 (約30毫秒) | — |
該架構為用戶提供 最大程度的控制和靈活性 — 您可以設計自己的協定棧, 加密, 或根據您的專案要求的身份驗證機制.
9. 結論
本質上, 我們的無線視訊數據鏈路充當 高性能, 低時延透明傳輸通道. 它保證您的資料按原樣傳輸, 無需更改或增加延遲.
對於需要額外的應用 安全, 正直, 或重播保護, 我們建議在 應用層或網路層, 讓您根據您的具體需求實現安全性和效能.





問一個問題
感謝你的回應。 ✨